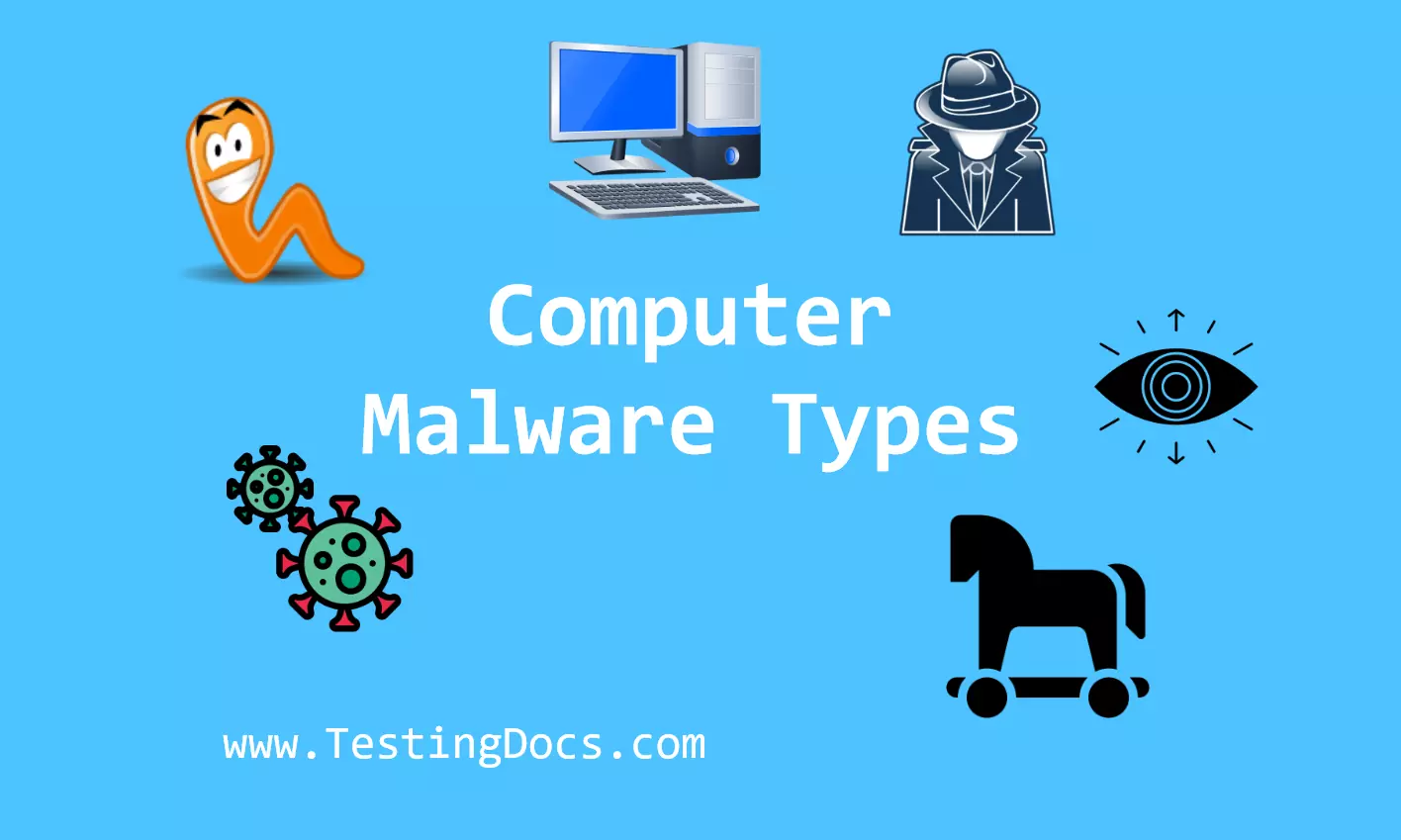
Types of Malware
Types of Malware
In this tutorial, you will learn about different types of malware. Malware is malicious software designed by hackers to damage or gain unauthorized access to a victim’s computer. Internet security is a serious issue for Internet users. It is very important to stay updated on the latest malware and hacking techniques. Some types of malware are as follows:
- Virus
- Trojan Horse
- Worms
- Ransomware
- Spyware
- Rootkits
Virus
A computer virus is a type of malware that attaches to another program and replicates itself and spreads from one computer to another in the computer network. Computer viruses are called viruses because they share some of the characteristics of biological viruses.
For example, a biological virus spreads from person to person, similarly, a computer virus spreads from one computer to another computer.
Trojan Horse
A Trojan horse is a type of malware that downloads onto a computer disguised as a legitimate program. Unlike viruses, Trojans do not replicate themselves, but they can be destructive. Some Trojans open a backdoor entry for the hacker allowing unauthorized access to the system. We can categorize trojans into many different types.
Worms
A worm is a type of malicious software (malware) that can replicate itself and spread across computers and networks without needing to attach to a program or file.
A worm is a type of malware that is self-contained software and can replicate to other computers using the computer network. Unlike viruses, worms do not attach themselves to other programs. Worms use computer networks and security vulnerabilities to replicate themselves.
Ransomware
Ransomware is a type of malware that allows a hacker to encrypt the data on the computer system. This makes the system unusable for the legitimate computer user(victim). The hacker demands the computer user pay money to unlock the computer system. Payment is usually demanded in cryptocurrencies like Bitcoins.
Spyware
Spyware is a type of Malware that gathers information about a person or organization without their consent and knowledge. Spyware is also called spybots. Spyware is tracking software that’s installed on someone’s computer to secretly gather information about the user, company, etc, and send it to interested parties. The main use of spyware is for espionage purposes.
Rootkits
Rootkits are designed to gain unauthorized access and gain administrative control over a victim’s system. Rootkits are mostly used for stealthy and persistent attacks.
Comparison of Virus, Trojan Horse, Worms, and Spyware
| Virus | Trojan Horse | Worm | Spyware | |
|---|---|---|---|---|
| Definition | A malicious program that attaches itself to a host file and spreads when the file is executed. | A program that appears legitimate but performs malicious activities in the background. | A self-replicating program that spreads across networks without user intervention. | Software that secretly gathers user information without consent. |
| Replication | Requires a host file to replicate. | Does not self-replicate. | Self-replicates across systems and networks. | Does not replicate, but installs itself silently. |
| Infection Method | Spreads via infected files, email attachments, or downloads. | Disguised as useful software; user installs it unknowingly. | Exploits system vulnerabilities to spread automatically. | Often bundled with free software or downloaded secretly from websites. |
| Damage Caused | Corrupts or deletes files, affects system performance. | Opens backdoors, steals data, installs other malware. | Consumes bandwidth, slows down networks, may install malware. | Tracks keystrokes, browser activity, personal data. |
| User Interaction | Needs user action to activate (e.g., run infected file). | User installs thinking it’s legitimate. | Spreads automatically without user interaction. | Operates silently without user knowledge. |